PointSet (Point Set Network) is a new generation of high-performance public chain with a multi-layer incentive mechanism as the core. Build a decentralized network system based on distributed technology. PointSet Chian is developed using the latest generation of blockchain technology, starting from the point set chain, focusing on digital identity, copyright protection, decentralized social and distributed content platforms, and will later expand to decentralized asset services, decentralized transactions, etc. aspect. Mainly used in the media and copyright fields. Point PAXOS consensus algorithm.
PointSet technology introduction
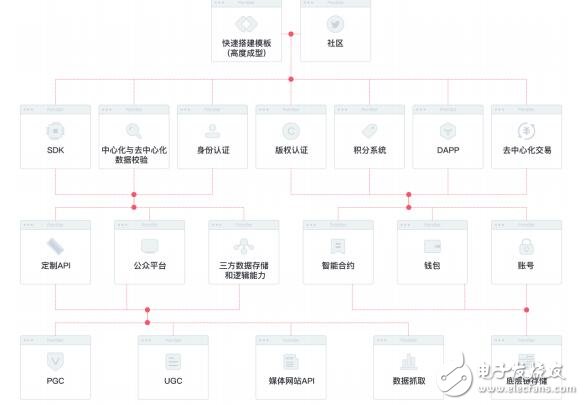
PointSet, as a bottom-level network, builds a decentralized network system based on distributed technology. From the multi-channel acquisition and high-performance storage of bottom-level data, to the processing of middle-tier data and on-chain recording, to the application layer providing APIs and SDKs, to build a bridge between the bottom-level data and the upper-level applications for developers and users, in terms of information exchange and value The transfer plays an important role. SET under the token economy model is the value transfer medium of the entire ecology, and the multi-layer mining mechanism can ensure the virtuous circle of the entire ecology.
1.SETChain
The PointSet chain uses the latest generation of technology development to provide comprehensive on-chain data records (identity authentication, copyright protection, incentive mechanism, etc.) for ordinary users, developers, websites, third-party partners, platforms, organizations and other multiple channels.
Each data on the PointSet chain is a Point, and countless points form a Set. The chain contains smart contracts, and developers can quickly build their own DAPPs; they can also be quickly integrated through PointDock on the upper layer of the point set network.
In addition to the existing main chain technology, PointSet has also created and improved a series of infrastructure including PointCheck, PointDock, and PointPaxos to protect the safety of ecological data.
2. Block
The composition of the SET block draws heavily on the structure of an excellent main chain, and includes the following parts:
a) ParentHash The hash of the parent block
b) stateRoot: the hash of the root node of the state number composed of transactions of the current finalized block
c) transactionRoot: the hash of the root node of the transaction tree
d) receiptRoot: the hash of the root node of the receipt tree
e) logsBoom: Bloom filter composed of indexable information in all transaction receipts
f) difficulty: package the difficulty scalar value of the current block
g) number: the number of ancestors of the block
h) TImestamp: timestamp of block initialization
i) extraData: Remarks on the current block
j) mixHash: 256-bit hash
k) nonce: 64-bit value (together with mixHash to prove whether the computational load is sufficient)
Both the transaction tree and the receipt tree are Merkle trees, Merkle trees:
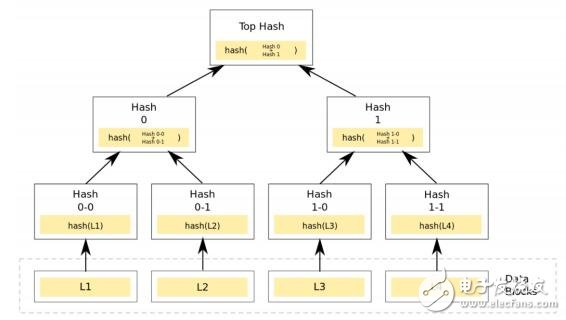
Merkle Tree can be regarded as the generalization of Hash List (Hash List can be regarded as a special kind of Merkle Tree, that is, a multi-fork Merkle Tree with a tree height of 2).
At the lowest level, like the hash list, we divide the data into small data blocks, and there are corresponding hashes corresponding to it. But going up, instead of calculating the root hash directly, it merges the two adjacent hashes into a string, and then calculates the hash of this string, so that every two hashes will get married and have children, and get Created a "sub-hash". If the total number of hashes at the bottom is singular, then a single hash will inevitably appear at the end. In this case, it is directly hashed, so its sub-hash can also be obtained. So pushing upwards is still the same way, you can get a smaller number of new level hashes, and eventually an upside-down tree will inevitably form. At this position of the tree root, there is only one root hash left in this generation. We call it Merkle Root.
Before the p2p network downloads the network, first obtain the Merkle Tree root of the file from a trusted source. Once the tree root is obtained, the Merkle tree can be obtained from other untrusted sources. Check the received Merkle Tree through the trusted root of the tree. If the MerkleTree is damaged or false, another Merkle Tree is obtained from other sources until a Merkle Tree that matches the root of the trusted tree is obtained.
The main difference between Merkle Tree and Hash List is that you can directly download and verify a branch of Merkle Tree immediately. Because the file can be divided into small data blocks, so if a piece of data is damaged, just download the data block again. If the file is very large, then Merkle tree and Hash list are both available, but Merkletree can download one branch at a time, and then verify the branch immediately, if the branch is verified
After the certificate is passed, you can download the data. The Hash list can only be verified by downloading the entire hash list.
Merkel trees can quickly locate changes in leaves, saving a lot of query time. The transaction state tree is the Merkel Patricia tree (MPT):
MPT (Merkle Patricia Tree), as the name implies, MPT is a mixture of Merkle tree and Patricia tree:
In the SET chain, we use a hexadecimal prefix code, there are 16 characters in the alphabet, one of which is nibble
The nodes in the MPT tree include empty nodes, leaf nodes, extended nodes, and branch nodes: empty nodes, which simply represent empty, are an empty string in the code.
Leaf node (leaf), expressed as a key-value pair of [key, value], where key is a special hexadecimal code of key, and value is RLP code of value.
The extension node (extension) is also a key-value pair of [key, value], but the value here is the hash value of other nodes. This hash can be used to query the nodes in the database. In other words, link to other nodes through hash.
Branch node (branch), because the key in the MPT tree is encoded into a special hexadecimal representation, plus the last value, the branch node is a list of length 17, and the first 16 elements correspond to the key If there is a [key, value] pair that terminates at this branch node, the last element represents a value, that is, the branch node can search for the end of the path or the intermediate node of the path.
Another important concept in the MPT tree is a special hexprefix (HP) encoding, which is used to encode keys. Because the alphabet is hexadecimal, each node may have 16 children. Because there are two kinds of [key, value] nodes (leaf nodes and extended nodes), a special terminator identifier is introduced to identify whether the value corresponding to the key is the real value or the hash of other nodes. If the terminator mark is turned on, then the key corresponds to the leaf node, and the corresponding value is the real value. If the terminator tag is turned off, then the value is the hash used to query the corresponding node in the data block. HP can encode it regardless of whether the key has an odd length or an even length. Finally, we noticed a single hex character or 4bit binary number, which is a nibble.
HP coding is very simple: a nibble is added to the key (prefix in the figure below) to encode the state and parity of the terminator. The lowest bit indicates parity, and the second lowest bit encodes the state of the terminator. If the key is an even length, add another nibble with a value of 0 to maintain the overall even characteristic.
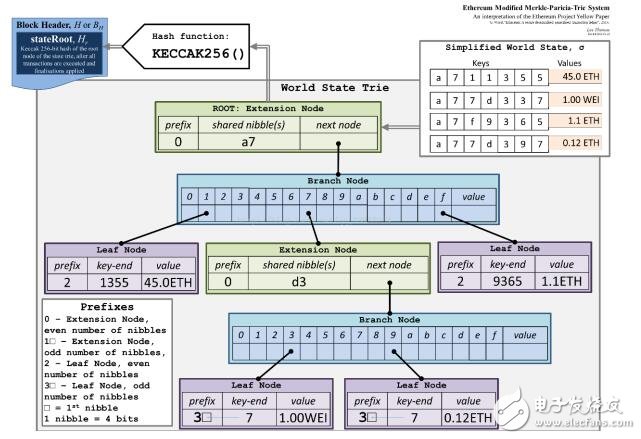
as the picture shows:
There are a total of 2 expansion nodes, 2 branch nodes, and 4 leaf nodes.
The key value of the leaf node is:
The prefix of the node:

The transaction tree, state tree, and receipt tree record the most important information on the block, which is also the core of preventing the block from being tampered with and facilitating verification.
Recording the hash of the parent block in this block is a necessary condition for the integrity of the entire chain.
3. SET incentive
Regardless of the pos or dpos consensus mechanism, we all need an incentive mechanism to maintain the normal operation of the entire main chain. We have designed a consensus method to transfer to one family. The PointSet main chain tail solves this problem and designed a built-in Currency—SET, all currencies running on the main chain of set are calculated with point as the smallest unit.
a) The smallest unit of Token is point, 1SET = 10^18point
b) The second unit is line, 1SET = 10^15 line
c) Then flat, 1SET = 10^12 flat
d) The largest unit is SET
4.PointCheck
a) PointSet has functions such as copyright verification and content recording. The data sources come from PGC, UGC, media and other channels. Adjusted to PointCheck on the basis of SimHash and SimHash, by judging the similarity of the copyrighted content submitted by the user, calculating its weight to reach a conclusion (whether the storage is legal and judging the corresponding reward).
b) SimHash calculates the similarity between two documents through the following process:
1) Word segmentation
Split the document into words, and then assign weights to each word (for example, you can use the tf-idf algorithm to calculate the weight, but here you need to change the algorithm to map the tf-idf value to an integer value with a monotonically increasing function)
2) Calculate Hash
3) Weighting
Multiply the word by the corresponding weight, and replace 0 with -1 to multiply the corresponding weight
4) Merge
Accumulate the word sequence bitwise from front to back
5) Dimensionality reduction
Change the result of the merge into a 0-1 string, the method is greater than 0-"1, less than 0-"0, so that each document will get an ID
6) Compare Hamming distance
Perform an exclusive OR operation between the result obtained after dimensionality reduction and the ID of each existing document, and then calculate the number of 1 in the operation result to obtain the Hamming distance.
The SimHash algorithm is efficient and suitable for distributed applications. It consumes little space, but when long and short documents exist at the same time, there will be misjudgments.
MinHash is very similar to SimHash in the previous processing, but obviously exceeds SimHash in the judgment efficiency of binary data
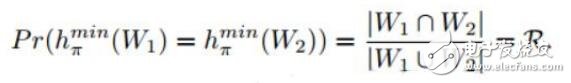
PointCheck takes the best from the two hash similar judgments. MinHash is used for binary judgment, and the others use SimHash. While improving efficiency, it also highly improves the accuracy of judgment.
5.PointDock
Point Dock is a complete access system. The Dianji network can not only connect to project parties and media platforms, but also access self-media and even ordinary users.
Point Dock has the following system:
a) Points system, even ordinary users can access the PointSet. After the identity is bound, the user or the platform can store the document on the PointSet at any time. After the PointCheck verification, the corresponding result will be obtained, and the corresponding result will be returned to you integral.
b) Self-media access, PointSet will open WeChat public account, Toutiao account and other media. After the identity binding, you can perform other operations such as copyright verification protection and bonus points.
c) Low-cost WEB construction. In order to facilitate third-party accessors to focus more on operations and other aspects of business, we have assembled a complete set of website templates, which will include PointSet's complete incentive system, identity authentication system, and copyright protection system, while using PointSet Ordinary users of the identity authentication system will also reduce registration costs, open up data, and achieve a perfect collection from Point to Set.
d) Ordinary developers, ordinary developers can access more customizable APIs, developers can only use the identity system to obtain PointSet users at zero cost, and can also selectively access the point set network’s credit system and copyright system And other modules.
e) In-depth cooperation with developers, PointSet will open more permissions to in-depth cooperation with developers to discuss the blockchain world together and create greater social value.
6. SET consensus mechanism
Since the pow consensus mechanism has always had the problems of wasting resources, low efficiency, and low TPS, we adopt the dpos algorithm that is faster, safer and less energy-consuming.
DPOS stands for Delegated Proof of Stake - it is a variant of Proof of Stake (Ethereum's PoS) that provides a high level of scalability at the cost of limiting the number of validators on the network.
According to this algorithm, people who hold tokens on the entire network of pointset can select block producers through the voting system. Once elected, anyone can participate in block production. It's a bit like the "People's Congress System". Ten super nodes are selected from all the nodes that join the pointset network, and then the pointset blockchain consensus is carried out between these super nodes. The existence of super nodes greatly improves the pointset chain. TPS.
In POW or other POS consensus, the nodes are not limited and the order of block generation is random. Any node that joins the pointset network will become a super node, and the super node needs all other ordinary nodes to vote. Of course, the super node Also has certain responsibilities:
1. Provide a server node to ensure the normal operation of the node;
2. The node server collects transactions in the network;
3. The node verifies the transaction and packs the transaction into the block;
4. The node broadcasts the block, and other nodes add the block to their own database after verification;
5. Lead and promote the development of blockchain projects;
If the super node cannot perform its duties on time, it will be replaced immediately, and other competing nodes with a high number of votes will be elected to efficiently maintain the normal operation of the pointset blockchain platform.
Byzantine fault tolerance solved by DPOS reduces the difficulty in two dimensions:
1. The number of nodes is fixed at only 21. And the node information is transparent.
2. Fix the block sequence. Each node is the same as the baton, one by one, the blocks are relayed down.
Each node cannot produce a block before it has its turn to produce a block. It must be their turn to produce blocks. If there is a block failure, this node will be skipped.
DPOS consensus process:As long as they can get votes from the token holders, anyone can participate in the block production process and have the opportunity to independently produce blocks. It is estimated that a block will be produced every 1.5 seconds on the pointset blockchain. At any time, only one producer is authorized to produce blocks. If the block is not successfully produced within a certain period of time, the block is skipped.
Using the Pointet client software full-node mode, blocks are rounded with 100 blocks (each producer can produce 10, and there are 10 producers, and the two are multiplied). At the beginning of every ten rounds, 10 block producers are selected through voting by token holders. The selected producers produce blocks in an agreed order, which is agreed upon by 10 or more producers.
In the pointset architecture, the block generation takes 10 blocks as a cycle. Before the start of every ten block generation cycles, 10 block producers will be voted for. The top 9 block producers are first selected automatically, and the 10th block producer is selected according to the probability corresponding to the number of votes obtained. The selected producer will be mixed according to the pseudo-random number derived from the block time. In order to ensure that the connection between block producers is as balanced as possible.
If the block producer misses a block and no block has been generated in the last 3 hours, the block producer will be deleted. By not arranging nodes that are not reliable enough, and reducing missed block creation as much as possible, the entire network can run more smoothly.
Under normal circumstances, the DPOS block chain will not experience any forks because block producers cooperate to produce blocks instead of competing. If there is a block fork, the consensus will automatically switch to the longest chain. The length of a blockchain with more producers will grow faster than a blockchain with fewer producers. In addition, no block producer should produce blocks on two blockchain forks at the same time. If a block producer finds out that it has done so, it may be voted out.
Transaction confirmation
Blockchains maintained by the DPOS consensus algorithm are generally 100% online. This means that a transaction will be written to the blockchain after an average of 0.5 seconds, and all the block producers will know the transaction at the same time. This means that in only 0.5 seconds, a transaction can be deemed 99.9% received by the blockchain.
Under normal circumstances, the DPOS blockchain is unlikely to have a fork, because the block production process is a cooperative process rather than a competing process. If a fork occurs, the consensus will automatically shift to the longest chain. This mechanism is effective because the rate at which a block is added to the blockchain is directly related to the number of block producers, and these producers have reached a consensus on the longest chain. In other words, if there are more producers in a forked blockchain, the length will be faster than fewer producers, because the number of missed blocks on the chain with more producers will be fewer. a lot of.
There are some extraordinary situations, such as software bugs, Internet congestion, or the appearance of malicious block producers, and the blockchain may fork. In order to ensure that a transaction is irreversible, you can wait for 10 block confirmations. According to the configuration of the pointset chain, it takes 15 seconds on average to confirm 10 blocks under normal circumstances.
Within 9 seconds of the occurrence of the fork, the block producer may discover the possibility of the fork and warn the user. When a node observes the network, if it finds two consecutive block loss events, it means that the change of the node is 95% likely to be on the forked branch of the blockchain. After 3 consecutive lost blocks, the node has a 99% chance of being on a forked blockchain. A predictive model can be generated that will use the information lost by the node, the recent participation rate, and other factors to quickly warn users of any problems.
The response to this warning depends entirely on the nature of the business transaction, but the simplest response is to wait for 7/10 confirmation until the warning stops.
Proof of Transaction (TaPoS)
pointset requires that every transaction include the hash of the most recent block header. This hash serves two purposes:
1. Prevent a large number of transaction records from appearing on the forked blockchain;
2. Enable the system to perceive whether the user is on the forked blockchain
Over time, all users eventually directly confirm the block chain, which makes it difficult to forge counterfeit chains because counterfeiting will not be able to migrate transactions from legitimate links.
The most basic principles of DPOS consensus:
a) Users will vote with weights based on the amount of voting coins in their hands, and according to the voting results, select the current super node to generate blocks according to certain rules;
b) At the same time, nodes that fail to run for super nodes, users who vote for the winners, and users who vote for the losers may all receive a certain amount of compensation to encourage them to continue participating in the subsequent election process;
c) Super nodes will pack blocks in sequence according to certain distribution rules and get the largest share of rewards;
d) The majority of the super nodes will be selected based on the voting results, and the rest will be guaranteed in accordance with a certain algorithm in the rest of the other nodes, all nodes are likely to be selected.
7. Smart contract
Smart contracts are all made up of codes, while a typical contract is a text with legal significance. Its biggest feature is that it cannot be changed and automatically executed. This forms the basis for smart contracts to achieve "anonymous credit".
Smart contracts have four main purposes: storing and maintaining data, managing contracts/relationships between untrusted users, serving as a software library to provide letters to other contracts, and supporting complex authority management. Everyone sees that it is very versatile, and it is not optimized for some specific applications, and the above features can be used in combination. This is what pointset has always insisted on, to be the most basic support for the code execution mechanism.
Blockchain smart contracts have three technical characteristics:
1. Data transparency
All data on the blockchain is open and transparent, so the data processing of the smart contract is also open and transparent, and any party can view its code and data at runtime.
2. Cannot be tampered with
All data of the blockchain itself cannot be tampered with. Therefore, the smart contract code deployed on the blockchain and the data output generated by the operation are also non-tamperable. The node running the smart contract does not have to worry about other nodes maliciously modifying the code and data.
3. Permanent operation
The nodes supporting the blockchain network often reach hundreds or even thousands. The failure of some nodes will not cause the stop of the smart contract. The reliability of the smart contract is close to permanent operation in theory, which ensures that the smart contract can behave like a paper contract. Effective all the time.
How smart contracts workThe smart contract module, pointset will implement its own virtual machine pvm based on Web Assembly. Users can develop their own smart contracts in various mainstream languages ​​c, c++, python, java, etc., so as to customize them to meet user needs. The smart contract finally runs on the virtual machine, and developers can implement complex and diverse functions to meet customized needs.
Developers will write code for smart contracts. Smart contracts can be used for transactions and/or any exchange behavior between two/multiple parties. This code contains some conditions that will trigger the automatic execution of the contract.
Once the coding is completed, the smart contracts are uploaded to the blockchain network, that is, they are sent to all devices connected to the network. In the case of another blockchain application-Bitcoin, it is like uploading network updates about Bitcoin transactions to the blockchain.
Once the data is uploaded to all devices, the user can reach an agreement with the result of executing the program code. Then update the database to record the execution of the contract and monitor the terms of the contract to check compliance.
In this way, a single party cannot manipulate the contract, because the control over the execution of the smart contract is not in the hands of any single party.
Compared with traditional contracts, smart contracts have many advantages:
i. Compared with traditional contracts, the biggest feature and advantage of smart contracts is that they solve the problem of "credit". Before the conclusion of a traditional contract, participants must first understand the credit background of the parties to select suitable objects. After the conclusion of the contract, they must also rely on the integrity of the parties, or introduce a third party (such as Alipay) to guarantee the performance of the contract.
ii. Smart contracts because the resources on the chain are true and transparent, the content of the contract cannot be changed after it is confirmed, and the execution does not rely on any additional operations. In the end, "anonymous credit" has become a reality. There is no need to conduct a credit investigation before the conclusion of the contract, and no third-party guarantee is required after the conclusion of the contract, thereby greatly reducing transaction costs and greatly improving transaction efficiency.
iii. The data of the smart contract cannot be deleted or modified, but can only be added. The history of the smart contract can be traced. At the same time, the cost of tampering with the contract or breaching the contract will be high, because its malicious behavior will be recorded forever and widely known.
iv. Decentralized smart contracts do not rely on third parties to execute contracts. Therefore, the potential benefits of smart contracts include reducing the costs of signing contracts, execution and supervision; therefore, for many contracts related to low-value transactions, this is a significant reduction in labor costs. The entire process of contract verification and execution becomes fast with direct transactions between users.
v. Smart contracts are not prone to problems such as power outages, node failures, floods and fires. When the smart contract is stored on the blockchain distributed ledger, there is no risk of misplacement or loss. This means that every device connected to the network has a copy of the contract, and the data will always be stored on the network.
8. CD (Controller-Data) mode
From a business perspective, smart contracts only need to do two things. One is how to define the structure of data and how to read and write, and the other is how to process data and provide external service interfaces.
In order to better implement module abstraction and contract structure layering, separating these two things is to separate business control logic and data from the contract code level. Such processing is the current practice in complex business logic scenarios. Considered the best model.
This mode is called CD (Controller-Data) mode for short. Divide contracts into two categories: Controller Contract and Data Contract.
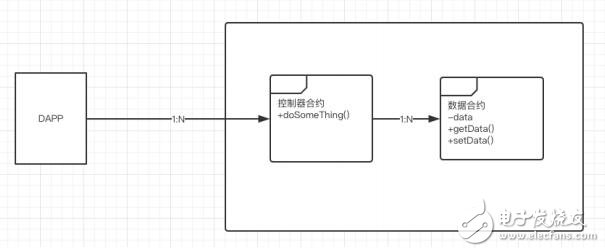
The controller contract obtains data by accessing the data contract, performs logical processing on the data, and then writes back to the data contract. It focuses on the logical processing of data and external services.
According to the different processing logic, there are common namespace controller contracts, proxy controller contracts, business controller contracts, factory controller contracts, etc. Under normal circumstances, the controller contract does not need to store any data, it completely relies on external input to determine the access to the data contract. In special cases, the controller contract can store the address or namespace of a fixed data contract (the contract address is obtained at runtime through the namespace).
The data contract focuses on the definition of the data structure and the bare interface for reading and writing the stored data. In order to achieve the purpose of unified data access management and data access authority control, it is best to expose the data read and write interface only to the corresponding controller contract. Prohibit other methods of read and write access. Based on this model, following a top-down analysis method, design various controller contracts from the externally provided service interface, and then gradually transition to the data model and storage method required by the service interface, and then design various data contracts. Complete the design of the contract structure relatively quickly.
9.SETRLP
RLP (Recursive Length Prefix) provides an encoding suitable for arbitrary binary data arrays. RLP is the main encoding method for serializing objects in the SET main chain. The only goal of RLP is to solve the encoding problem of the structure; the encoding of atomic data types (for example, string, integer, floating point) is handed over to higher-level protocols; we stipulate that the number in SET must be a big-endian word Sectional storage format with no zero space (that is, an integer 0 is equivalent to an empty array). For the problem of encoding a dictionary data in the RLP format, there are two suggested ways. One is to express key-value pairs through a two-dimensional array, such as [[k1, v1], [k2, v2]. ..] and lexicographically sort the keys.
10.SET network protocol
The decentralization of blockchain technology relies on the underlying networking technology. The bottom layer of PointSet implements p2pServer, which can be roughly divided into three layers.
a) The underlying routing table. Encapsulates functions such as kad routing, node data structure and calculation records, node search, and verification.
b) Middle-level peer abstraction, message open sending interface, server externally provides peer detection, initialization, event subscription, peer status query, start, stop and other functions.
c) The top layer of PointSet is the peer, and the peerset is re-encapsulated. Through the Run function of the protocol, when the peer is started in the middle layer, the peer is obtained, and finally the stable peer is intercepted through a loop and packaged for use in the peerset.
Underlying routing tableSimplify the problem here and only discuss the Node Discovery Protocol. This layer maintains a bucket, with a total of 17 buckets, each with 16 nodes and 10 replacement nodes. The distance between hash and localNode must be calculated first when Node is placed. Then select a bucket according to the distance and put it in. When taking it, calculate the target and the objects in each bucket one by one. For details, please refer to the closest function, which will be posted later.
The distance formula satisfies: f(x,y)=256-8*n-map(x[n+1]^y[n+1]) Note: n is the same number of nodes and map is a negative correlation mapping.
Simply put, the more similar, the smaller the value.
The most important of these is the table object. The public methods of table are:
a) NewTable instance creation
b) Self local node acquisition
c) ReadRandomNodes reads several nodes randomly
d) Close
e) Resolve finds a node in the surrounding
f) Lookup to find the neighboring nodes of a node
11.SETRPC
RPC stipulates that both parameters and return values ​​are serialized into binary data during network transmission. This process is called serialization (Serialize) or marshal (marshal). Send the serialized binary to another server through addressing and transmission. After the other server receives the binary data, it will deserialize and return to the expression in memory, and then find the corresponding method call to return the return value to the first server in binary form, and then deserialize and read the return value .
PointSet network (PointSet) application scenarios1. Digital Identity
Personal information in the Internet age is not reasonable enough in terms of privacy, security, and ease of use. In the Dianji network, individuals can create their own identity, fully control and guarantee the authenticity and security of the identity. Personal digital identity is a key to open the blockchain world. With this key, users can use it to sign agreements, protect copyright, participate in voting, and trade assets.
2. Copyright protection
The emergence of the Internet has greatly accelerated the speed of information dissemination, but it has also brought some side effects. Under the current Internet economic model, copyright protection has always been the focus of the Internet era. The lack of copyright protection has caused difficulties in copyright protection, copyright proof, and copyright protection.
Using Dianji Chain and Dianji Identity System, Dianji Network provides a safe, convenient and low-cost copyright protection system. In the Dianji network, content producers can establish their own unique digital signatures through the identity system. After the work is bound to the digital signature, these immutable records are stored in the decentralized underlying network, so that the copyright of the content producers can be obtained. Chain recognition is convenient for copyright proof and rights protection.
3. Distributed social network
In Dianji's decentralized social network, users can control their own data. Using the digital identity system, users can run their own nodes to access the network, link between nodes in real time, and store user information end-to-end encrypted on the public chain. , Social information is redundantly stored on the public chain, and this information can only be viewed by the holder of the private key. Dianji distributed social network returns user information control to users to protect user privacy.
The token incentive mechanism can motivate users to create more value. As a data platform, Dianji Network can realize point-to-point communication between users and users without the intervention of a third party. Users can choose normal communication between friends, or choose to chat anonymously, or create a community on the platform. It is entirely up to the user who controls the private key.
4. Distributed content platform
The traditional media economic model is composed of users, authors, platforms, and advertisers, and the needs of each party are not uniform. Users can use platform functions to meet the needs of information, relationships, etc., but users have no control and profit rights over the platform. In the entire economic system, users are always in a passive state.
The dot-set network weakens the concept of roles of all participants. Under the premise of maximizing the interests of participants, role identities can be transformed into each other. In addition to providing APIs and other interfaces for developers, the token incentive mechanism is used to propose a brand-new concept-users are all. Users are both producers and consumers, as well as advertisers. The users participating in the development and construction of the bottom layer can also be the platform side, which is in line with the decentralized spirit of everyone participating in the blockchain.
Using Dianji can build a decentralized content production and incentive ecological network, so that content producers, content consumers, content platform parties and advertisers can allocate resources in a reasonable manner and obtain reasonable returns. Dianji Network has very broad prospects in terms of copyright protection, user needs, and advertising.
5. Other application scenarios
Decentralized asset service
Decentralized transaction
Decentralized insurance
Flow on the asset chain
Commodity traceability
Charity
PointSet is a public chain under a multi-layer mining mechanism, with the point set chain as the starting point. The main applications are digital identity, copyright protection, decentralized social and distributed content platforms, and will be expanded to decentralized asset services and decentralization. Transactions and other aspects. In the future, Dianji Network will integrate cross-chain storage functions and will bring a qualitative leap to the entire system.
Token incentive1. PointSet token SET
The ecological establishment of Dianji Network is inseparable from the token incentive mechanism. SET is a token in the dot set network, and the total amount will never be issued.
30% of the SET is used to build an ecological mining pool. Ecology is the foundation of the Dianji network. The Dianji network uses the original dynamic algorithm SET Method (combined with Delphi Method+ahp method) to distribute the mining income according to the weight of the developer’s ecological contribution value, thus operating the two-tier mining mechanism of the Dianji network. And token destruction mechanism. Each year, 10% of the remaining amount of the ecological mining pool is unlocked, that is, 630 million unlocked in the first year, 567 million unlocked in the second year, and 510 million unlocked in the third year...
20% of SET is used for team motivation. PointSet is a long-term planned project. The foundation has customized a ten-year team share thawing plan: in the first year, 0 will be thawed, and 10% of the team share will be thawed every year from the second year, that is, 420 million will be thawed every year.
20% of the foundation's share is used for commercial cooperation and ecological development. The remaining 30% is used for token exchange and candy distribution.
All ETH exchanged by SET is used for project construction. Including development team talent introduction, market expansion, community operation, etc.
2. Destruction mechanism
The original intention of SET is to be a small deflationary incentive token. Under the premise that no additional issuance will be made, a certain percentage of commission will be charged for the income of the dapp in the PointSet ecosystem, and this part of the commission will also be destroyed according to the proportion. Ensure the deflationary properties of the system.
A TPU Screen Protector made of the super toughness of the honeycomb structure. Its unique ultra-soft properties allow it to cover the most complex curves and contours in a device.
The self-healing design of the Hydrogel Screen Protector can protect the display screen of the device from damage, leave no air bubbles, and maintain the sensitivity of the touch screen. Advanced anti-fingerprint and dust- and oleophobic overlays keep your screen smudge- and dirt-free. This overlay is also important in providing maximum touch sensitivity for improved high-speed glide and optimal touch response.
The optical transparency of the Hydrogel Film is more than 90%, showing you the most original screen color and bringing the most realistic visual experience.
If you want to know more about the product information of the Hydrogel Screen Protector for OPPO, please click the product details to view the parameters, model, picture, price and other information of the OPPO Screen Protector.
Whether you are a group or an individual, we will do our best to provide you with accurate and comprehensive information about Hydrogel Screen Protectors!
Screen Protector For OPPO,Hydrogel Screen Protector for OPPO,TPU Screen Protector for OPPO,Hydrogel Film for OPPO,OPPO Screen Protector
Shenzhen Jianjiantong Technology Co., Ltd. , https://www.jjtbackskin.com